Home
Welcome to the AIHS Group!
AIHS (pronounced ‘ace’) is the Artificial Intelligence and Human Systems Group.
Head of Group Professor Effie Lai-Chong Law
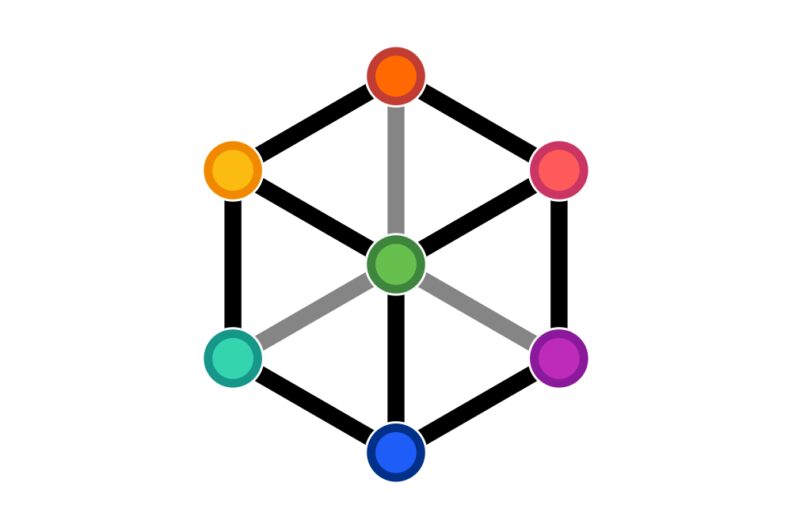
AIHS has five major research themes that share the core goal of applying AI for social good. All themes are working on real-world problems with a tangible impact on people’s lives while focussing on different research areas and methodologies:
- Digital Humanities
- Digital Health
- Human-Computer Interaction
- Software Engineering
- Technology-Enhanced Learning
In addition, AIHS is involved in the N8 Research Partnership and N8 CIR groups and many AIHS members are part of the EquiAI network.
We build inter-disciplinary collaborations within Durham and the UK as well as internationally, boast connections to the industry and welcome companies looking for research solutions to their problems.
